 Featured
Featured
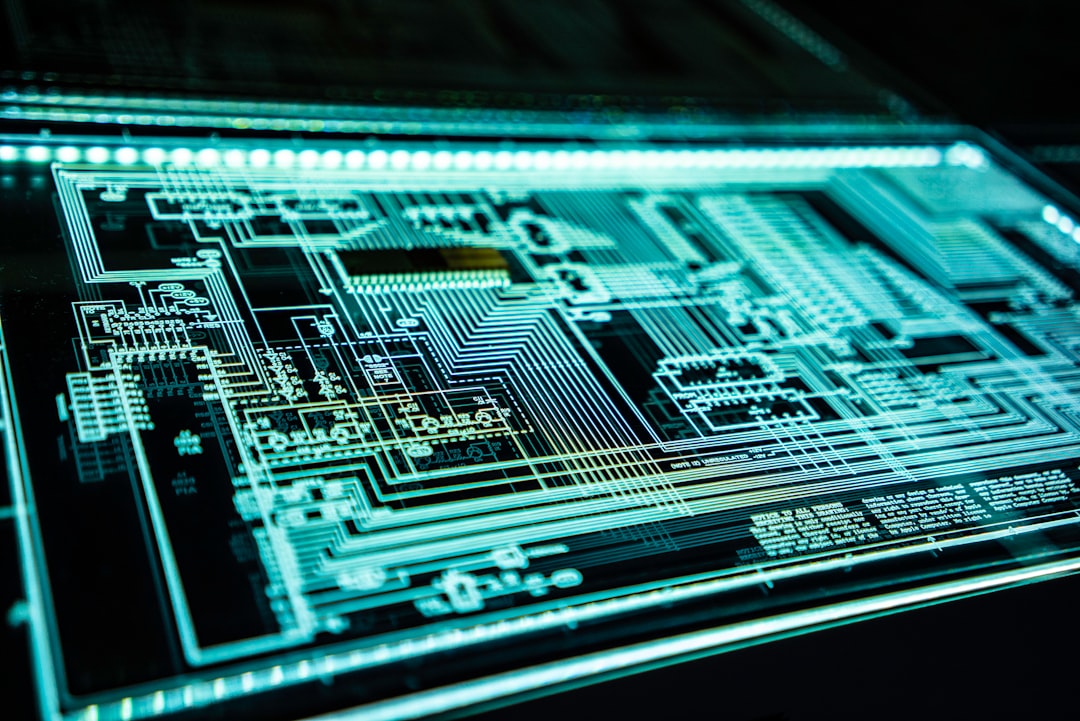
Zero Trust Architecture Implementation Guide
Discover how to implement Zero Trust security models in enterprise environments. Learn about identity verification, micro-segmentation, and continuous monitoring strategies that protect against modern cyber threats in 2025.
Continue Reading


